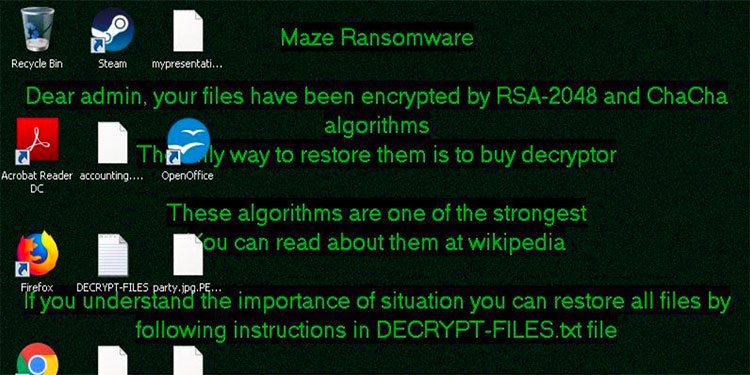
According to researchers with Sophos Managed Threat Response, the operators behind Maze ransomware have been adopting tactics from rival cybercrime organizations, adding a dangerous new feature. Maze …
Continue Reading about Maze Ransomware Adopts Ragnar Locker Virtual-Machine Approach