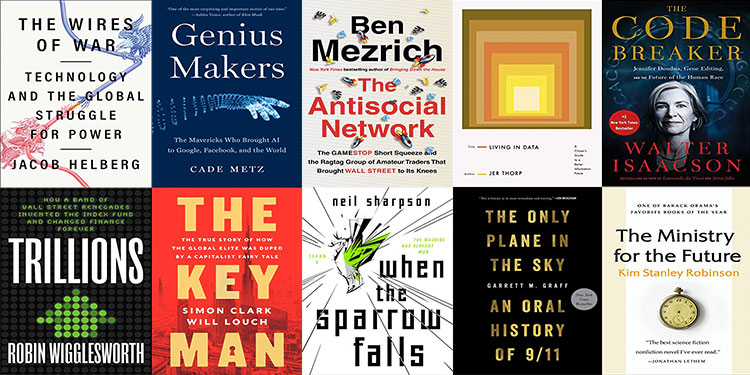
In this OODAcast, we talk with Simon Clark. Simon a British journalist and writer. He previously worked at the Wall Street Journal. His investigative reporting has led him to the poppy fields of …
Continue Reading about Simon Clark on Investigating the Key Man and a Billion Dollar Fraud