This week's OODAcast is with Kim Zetter, an incredibly well respected journalist who has been covering cybersecurity related issues for two decades. Matt Devost talks with Kim about a wide variety of …
Nate Fick on Dynamic Leadership and Adapting to Change
Nate Fick's career has been eclectic, but with a common element of demonstrating superior leadership abilities in a diverse array of successful opportunities. Nate is currently a General Manager at …
Continue Reading about Nate Fick on Dynamic Leadership and Adapting to Change
China’s Plan for Countering Weaponized Interdependence
In an article entitled "The international environment and countermeasures of network governance during the "14th Five-Year Plan" period" by Xu Xiujun (徐秀军) in the February 27, 2021 edition of China …
Continue Reading about China’s Plan for Countering Weaponized Interdependence
The OODA Almanac – 2021 Edition
As a logger and holstein farmer, my grandfather was heavily dependent on the weather for his livelihood. Each year, he purchased a copy of the Old Farmer’s Almanac and it was kept in an easily …
Michele Wucker on Identifying and Confronting the Obvious Risks of Gray Rhinos
Michele Wucker is specialist in risk management and crisis anticipation and is author of the book "The Gray Rhino: How to Recognize and Act on the Obvious Dangers We Ignore". While we've all become …
Former CIA Officer Rob Richer on the Geopolitical Landscape, Leadership Lessons Learned, and Supporting Decision-makers
Rob Richer is a highly regarded advisor to international executives and global government leaders including several heads of state. Rob has a well informed perspective on international risks and …
Camila Russo on Ethereum and the Future of Decentralized Finance (DeFi)
This week's OODAcast features an interview with Camila Russo, the author of the book "The Infinite Machine: How an Army of Crypto-hackers Is Building the Next Internet with Ethereum". Camila is also …
Continue Reading about Camila Russo on Ethereum and the Future of Decentralized Finance (DeFi)
Ric Prado on Intelligence Operations and a Legendary Career in the CIA
Ric Prado has been described by CIA leadership as the closest thing to 007 that the United States has ever had. Ric's life is packed with more adventure and operations than your favorite spy novel …
Continue Reading about Ric Prado on Intelligence Operations and a Legendary Career in the CIA
OODA Loop Greatest Hits – 2020 Edition
Each year we compile a list of our top posts based on page views. It provides interesting insight into what topics were top of mind for our Members. Obviously, Covid was a key interest area, but we …
Continue Reading about OODA Loop Greatest Hits – 2020 Edition
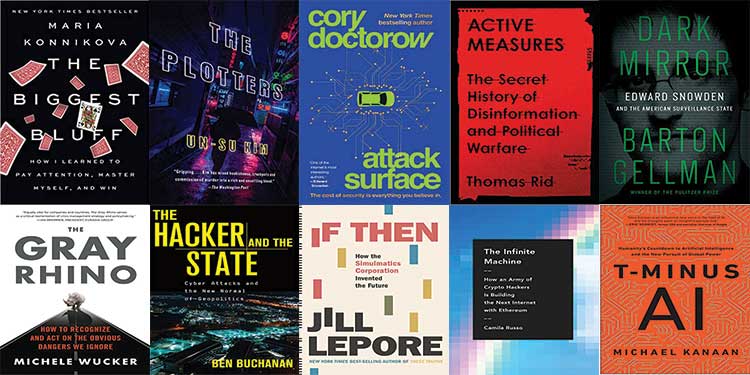
Top 10 Security, Technology, and Business Books of 2020
It was a challenging year for my booklist. Beyond just the 2020 pandemic issues, I had a hard time narrowing down on thematic for this year, so the list is even more eclectic than usual. I'm still …
Continue Reading about Top 10 Security, Technology, and Business Books of 2020