In 2019 Congress passed legislation signed into law by the President establishing the U.S. Cyberspace Solarium Commission, chartered to develop a consensus on a strategic approach to defending the US against cyber attacks of significant consequences. The commission was established to be bi-partisan and also staffed and chartered to be as informed as possible by experts who really know the state of technology and cyber defense today. The commission executed its charter through extensive outreach and dialog with leaders in industry, academia, non-profits and government and produced deliverables that will make a positive change in our nation’s defense.
For context, I’ve read cybersecurity policy documents, including strategies, commission reports and studies since being pulled into the cybersecurity world in 1998. And through volunteer work with the Cyber Conflict Studies Association (CCSA) have had an opportunity to dive deep into the history of cybersecurity policies. In my opinion, the product of the Solarium Commission beats every strategy document I have ever read for its logical foundations and actionable recommendations. Based on that and the level of dialog underway already in the executive branch and congress it appears this report will have a far reaching and long lasting impact.
But what do you need to know about this document? In this post I provide what I regard as the most critical components of the strategy and recommendations for action by business leaders seeking competitive advantage in the market.
High Level Summary of the Solarium Commission Recommended Strategy:
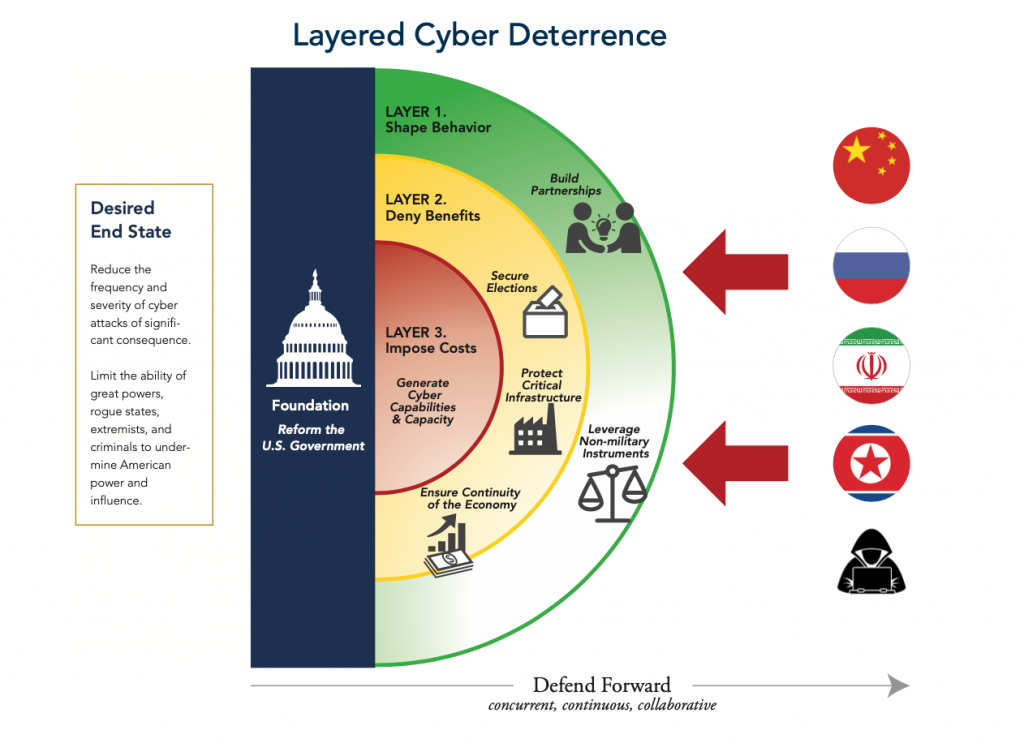
The United States will promote responsible behaviors in cyberspace, deny benefits to adversaries, and impose costs to any who attack.
Executive Level Take-Aways:
The commission did a good job at articulating the threat to the nation from cyber attack, providing solid summaries of threats from Russia, China, Iran and the DPRK as well as many criminal elements. A well informed discussion of our nation’s dependence on technology was also provided, resulting in a net assessment that change is absolutely imperative.
The overall conclusion of the report is summarized as a need for “layered cyber deterrence” to reduce the probability and impact of cyberattacks of significant consequence. There are three key components of this approach:
- Shape behavior: The United States must work with allies and partners to promote responsible behavior in cyberspace.
- Deny benefits: The United States must deny benefits to adversaries who have long exploited cyberspace to their advantage, to American disadvantage, and at little cost to themselves. This new approach requires securing critical networks in collaboration with the private sector to promote national resilience and increase the security of the cyber ecosystem.
- Impose costs: The United States must maintain the capability, capacity, and credibility needed to retaliate against actors who target America in and through cyberspace.
The report has a very clear appreciation of the fact that government must reform itself to meet the needs of the future. This includes actions for both the legislative and executive branches.
The actions and recommendations above are summarized graphically as:
Another key theme of the commission’s report is an understanding that in an open society like ours, government is not in command of industry or its citizens, it is supposed to be the other way around. Which means government must resist the urge to try to dictate solutions to everyone. Government has critically important roles to play, but influencing what industry, academia and citizens will require getting the government’s house in order and being a good example, which is not the case at this time. The many other actions for the government to take outlined in the report can help defend and deter the nation and also put in place mechanisms to ensure that when government regulation of industry and academia are required it is well thought out and done with appropriate citizen oversight and engagement.
There are other recommendations for changes that apply to industry, including changes to the law that will make it easier for organizations to be sued if they do not exercise appropriate duty of care when designing and fielding connected/digital products. This could clarify gaps in current US law for establishing liability for security vulnerabilities in software, hardware and firmware. Selling products with known security vulnerabilities or that could cause consumers harm would likely constitute unfair practices that result in enforcement actions if this recommendation is adopted.
Recommendations For Business Executives:
- It is important to remember that this report was focused on reducing the threat of major attacks and mitigate risks to the nation, not to individual businesses. There is some overlap of those topics of course, but nothing in this report should be interpreted as the government coming to save your business from cyber attacks. It is still your responsibility to defend your interests and reduce risks. You must still be proactive in your cyber defense if you want to succeed in the market.
- As a follow-on point: Do not try to defend your organization by yourself. No organization of any size can do that. Even the very largest firms coordinate and collaborate and outsource to experts. The art form here is finding the right balance between your internal defense capabilities and your outsourced security providers (OODA operates in this space and can provide you with recommendations on the right firm for your needs, reach out for a discussion if we can be of assistance).
- Understand that there are things you can do that are relatively low cost but make it much harder for adversaries to put your business at risk. For example, by configuring your networks and systems to enable a software defined perimeter you can make your internal assets almost invisible to outside attackers. By implementing multi factor authentication you can significantly impede the ability of adversaries to steal and use legitimate credentials. by implementing deception platforms you can detect when adversaries do breach your security and learn valuable information on them as you slow them down so you can appropriately respond. And by engaging experts to evaluate your security posture you can view your systems like adversaries would and proactively put smart security measures in place.
- Stay agile in your defense. Depending on the sector your business is in you already have legal and regulatory regimes you must comply with. The Solarium report is going to change legislation and some of that will impact your compliance requirements. But understand that your adversaries also track compliance requirements and they will attack you anyway! Compliance does not equal security. Agile defense informed by knowledge of your adversaries is the approach.
- Understand that your employees are really your first line of defense. Their training and education in spotting attacks and attempts to deceive them can provide you with early warning and make things harder on the bad guys. Your technical team will need more specific and dedicated training in cybersecurity to ensure shortcuts are not being made and technical debt is not being accumulated.
- If your business provides products or services in the cybersecurity space you really need to read the full report in its entirety. It is long (182 pages) but captures every major policy issue and topic facing the nation in cybersecurity. You will want to be fluent on these issues so you can engage in conversations with your customers and potential customers on these topics. The same is true if your company provides any service to the federal government. Read the full report at: https://www.solarium.gov/
- Any business that produces or assembles technology hardware, software, firmware or integrations of these should very carefully track legislation coming from the recommendations from the Solarium Report and seek legal counsel regarding its applicability to you. As you do, be sure you are working with lawyers who have past performance in cybersecurity issues.
- If you or your business has an opinion on the Solarium Report we strongly suggest you let it be known and become part of the national conversation underway today on this report.
- We also recommend executives take action to stay aware of the changing nature of the cyber threat (if you have not already done so, sign up now for the OODA Daily Pulse)
We are changing our approach to several topics based on the Solarium report, including updating our reporting on topics for our members. We would welcome your inputs as we do this. Please contact us with your insights, questions or comments.
Related reading
- All Done Except The Coding: Matt Devost, Jeff Moss, Neal Pollard and Robert Stratton on the May 2011 International Strategy for Cyberspace.
- OODA Video: A Practitioner’s View of the Cyber Threat: A member only on demand video threat brief.
- OODAcast with Congressman Will Hurd: Matt Devost interviews one of the most informed policy makers in congress.
- Cybersecurity Sensemaking: OODA’s collection of cybersecurity references.
- Geopolitical Sensemaking: More insights into key threat actors.
- Cyberwar Was Coming:A Reflection on the 25 Year Old Thesis that Predicted a Generation of Cyberconflict
- Deception Needs to be an Essential Element of Your Cyber Defense Strategy
