The establishment of the Space Information Sharing and Analysis Center (ISAC) was announced earlier this year with the mission to enhance the space community’s ability to prepare for and respond to cyber vulnerabilities, incidents, and threats. Although the Space ISAC won’t be fully up and running until early 2020, the industry group is already pursuing a hefty agenda item: lobby the federal government to designate commercial space systems as critical infrastructure (CI). While a partnership with federal agencies provides undeniable value, I do not believe the establishment of a new CI sector will result in the prioritized government action that industry is seeking.
In this article I explore the evolution of the CI program, benefits and concerns associated with a CI designation, and potential paths forward for the public and private sectors.
How the Critical Infrastructure Program Came to Be
Though the term “critical infrastructure” is relatively new, the formulation of CI strategy can be found throughout history. Populations have routinely made efforts to secure their own essential systems and services, as well as identify ways to target that which belongs to an adversary. In ancient Greece we witnessed Spartans initiate a blockade on the port of Piraeus during the Peloponnesian War. This maneuver closed off the primary grain route for months, causing Athens to starve. The weakened city was unable to effectively fight back and ultimately surrendered. In World War II, Allied military planners deliberately targeted vital nodes in the Axis industrial base and economic system. By attacking these structures, Allied planners believed they could achieve victory at a comparatively low cost due to the resulting destruction of the Axis war economy and civilian morale.
Remnants of World War II planning concerns could be found in the definition of CI outlined in Presidential Decision Directive 63 (PDD-63). Issued in 1998, PDD-63 was a cornerstone in critical infrastructure policy. It framed the issue of CI in terms of U.S. vulnerability to potentially devastating asymmetric attacks on physical foundations of national power. The directive emphasized the threat to military and economic security as adversaries pursued “non-traditional” attacks within the homeland.
Over time, CI policy has continued to shift incrementally. Major events in the U.S.—such as Hurricane Katrina—have expanded the definition and scope of CI to seriously take into account threats from natural disasters. Current CI policy also focuses on prosperity, public health, and civic life in addition to the longstanding concentration on military and economic security. However, the most substantive change has been the evolution from critical infrastructure protection (CIP) to critical infrastructure resilience (CIR). CIP calls attention to the identification, prioritization, and protection of infrastructure assets. Here we evaluate the most critical assets as ones that produce greater degrees of loss or disruption of service to fundamental facets of society, economy, or government function. CIR, on the other hand, focuses on hazard mitigation and recovering from emergencies in order to ensure the availability of essential services. In other words, policymakers have placed a growing emphasis on the resilience of key services instead of solely focusing on the protection of individual strategic assets.
As policy advanced, Presidential Policy Directive 21 (PPD-21) was released in 2013 and formally established 16 CI sectors that contributed to national resilience efforts. PPD-21 operates as an organizing framework for public-private partnerships where the Secretary of Homeland Security has overall responsibility for the coordination of the partnership activities. Nevertheless, a number of other federal agencies may be designated lead as Sector-Specific Agencies. These agencies are “responsible for providing institutional knowledge and specialized expertise as well as leading, facilitating, or supporting the security and resilience programs and associated activities of its designated critical infrastructure sector in the all-hazards environment.” This directive remains influential for CI risk management planning regarding the security and resilience of critical national resources.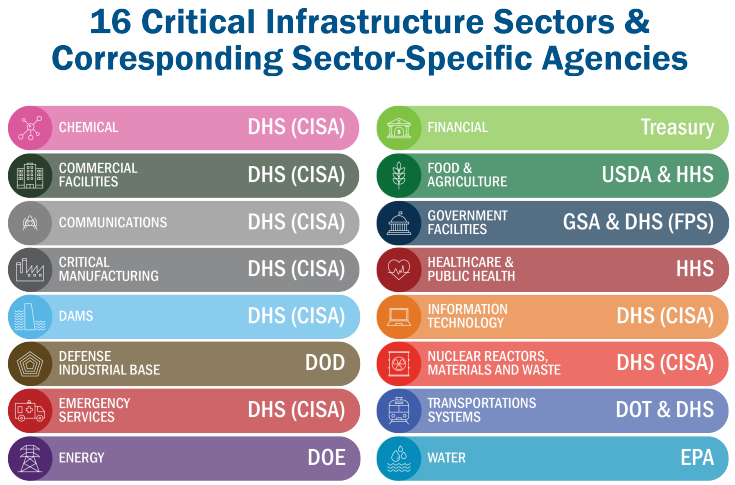
Benefits of a CI Designation
The CI program boasts a number of benefits, but in my opinion, the following five offerings are the most valuable.
First, the establishment of a new sector or sub-sector typically results in the formation of Sector Coordinating Councils (SCC) and Government Coordinating Councils (GCC). SCC membership is intended to be wide ranging where CI owners and operators convene CISOs, CTOs, general counsels, risk managers, compliance officers, and government affairs staff to collaborate with the government on security and resilience initiatives. GCCs provide the same function to the private sector, but are made up of Federal and State, Local, Tribal, and Territorial government representatives. They may include law enforcement, intelligence agencies, Federal regulators, and even White House officials. The sector partnership model allows for broad, nationwide participation and aims to reduce geographical or bureaucratic information sharing stovepipes.
A second perk of the CI program is the benefit of protected communications. Even though SCCs have an advisory relationship with the federal government, they are able to take advantage of certain exemptions. In essence, this allows the CI community to discuss sensitive information to mitigate vulnerabilities without the traditional requirement to hold public meetings. Additionally, DHS established the Protected Critical Infrastructure Information (PCII) program to safeguard sensitive CI information voluntarily shared with the government. PCII is not subject to the Freedom of Information Act and cannot be used in civil litigation or for regulatory purposes. These programs intend to encourage information sharing, while offering assurances that the government will not expose sensitive or proprietary data.
Third, a CI designation allows members to receive prioritized cybersecurity assistance from DHS. The department offers a range of cybersecurity assessments designed to evaluate an organization’s operational resilience. These are offered at no cost and on a voluntary basis. DHS has also touted the development of joint exercises with sectors to improve cyber incident response capabilities.
Fourth, DHS sponsors security clearances for “appropriate representatives of sector coordinating counsels, sector information sharing and analysis organizations, owners and operators of critical infrastructure, and any other person that the Secretary [of Homeland Security] determines appropriate.” Known as the Private Sector Clearance Program, it allows individuals who are responsible for the protection, security, and resilience of CI assets to receive classified threat information to make more informed decisions.
Finally, the most significant benefit comes from the associated norms around responsible peacetime state behavior. In international forums, the U.S. has taken the position that “[a] State should not conduct or knowingly support online activity that intentionally damages critical infrastructure or otherwise impairs the use of critical infrastructure to provide services to the public.” Also, a series of policy and legal documents have been issued under President Trump that signal greater consequences for those who target U.S. CI, including the option for military response.
Concerns with Establishing Space as a Standalone Sector
Even with the benefits outlined above, it is not entirely clear why commercial space systems require a standalone CI designation and I have yet to see a detailed argument in favor of one. Before going further, I want to be clear that I am not contesting space as a powerful domain. Economic, political, technological, and national security trends indicate that space is gaining more traction and U.S. leadership will be vital during this pivotal time. However, that logic does not always warrant a CI designation. Commercial maritime systems and artificial intelligence programs are not a standalone CI sectors. When evaluating commercial space, there are a handful of outstanding questions that need to be addressed first. Stakeholders should recognize there are alternative options available if the goal is for industry to receive priority assistance from the federal government.
The most important matter to address is, what is the scope of a new CI sector? Commercial space systems encompass a large swath of the industry, where not all facets may qualify as critical. Space assets are spread out through multiple existing sectors such as communications, critical manufacturing, and the defense industrial base. What are the benefits to rearranging components of existing sectors into a separate bucket versus formalizing new lines of effort in existing structures? Take for example the transportation sector which consists of seven sub-sectors: aviation; highway and motor carrier; maritime transportation system; mass transit and passenger rail; pipeline systems; freight rail; and postal and shipping. As commercial space travel becomes a reality in the next few years, would the industry receive more utility from remaining in this sector? (Especially since regulators of the U.S. commercial space transportation industry are already present within the transportation sector.) The lack of clarity in scope will only lead to greater confusion and inefficient government assistance.
A second consideration for industry is whether the sector structure is an inefficient model. PPD-21 operates as an organizing framework for public-private partnerships. The CI model works well for coordination efforts and information sharing, but it has proven shaky on quantifiably reducing risk. A report by the Congressional Research Service (CRS) assessed the CI partnership system and identified some notable concerns. First, the CRS report cited a study from 2013 that found “fewer than half of the 16 CI sectors had strong ‘communities of interest’ that actively engaged in CIP issues through [CI] partnership structures.” Communities of interest were strongest when industry was facing specific threats in their sector. This is something that may be diminished by a catch-all space designation. Second, while the study captured the early years of the CI program, the CRS report states that DHS has still not been able to systematically collect data about its effectiveness. As a result, the Department is unable to meaningfully assess improvements in CI security and if the partnership model has led to advances in national level (as opposed to enterprise level) resilience.
Additionally, with the unveiling of DHS’s National Critical Functions (NCFs), are CI sectors becoming antiquated? The NCFs attempt to take a risk management approach to holistically evaluate interconnected risks and dependencies. DHS claims this will help build a new “language” to discuss CI risk management and prioritize areas of national risk. NCFs should be something to watch out for, as the CRS report states, “CI policymakers have lowered the threshold of criticality to include infrastructure-related events with disruptive, but not necessarily catastrophic, effects at all levels of society and government.” CI sectors are running the risk of becoming overly saturated, where not everything designated as critical meets the threshold. As the policy continues to expand, the more difficult it will be to prioritize action since CI policy operates as a highly distributed enterprise that competes for limited federal resources.
Lastly, the benefits of a CI sector are not always as they seem. Bidirectional information sharing between the private and public sectors remains a challenge. Classified information sharing is even more difficult, as many CI companies are owned by foreign investors, which is a red flag during the security clearance process. Moreover, the U.S. response to provocation of domestic CI has generally been lukewarm. For instance, research shows that Russia has attacked the U.S. energy grid since 2013, yet public attribution and sanctions were not issued until five years later. If consequences against our most critical systems are not swift and costly, establishing new CI sectors will subsequently identify them as high-profile targets with a relatively low risk of retaliation.
Potential Ways Forward
If the Space ISAC is seeking greater security contributions to commercial space systems from the federal government, the following alternative options are available in lieu of a CI designation. These options identify potential risk management approaches and should be carefully assessed based on industry needs and government resources.
One option for the federal government would be exploring the utility of one or more sub-sector designations, as opposed to space as a standalone sector. I have already mentioned the transportation systems sector as a likely venue to account for human spaceflight activities. Critical manufacturing could be expanded to include commercial space requirements as well. Refreshing the existing sub-sector model may provide better resources and institutional knowledge for emerging space ventures, as opposed to piecing together a new sector.
Alternatively, the government could forgo the creation of a sector/sub-sector and instead bring together existing sectors into a new working group. DHS has already tested this method through the establishment of a tri-sector working group across the financial services, communications, and electricity sectors to analyze systemic risk and prioritize risk management activity. A similar model would work for commercial space systems, allowing the creation of fresh collaborative channels without the bureaucratic process of upending the existing sector structure.
The option with the quickest result would be to recruit key agencies into the Space ISAC. The current representation leans heavily on defense and intelligence agencies, but the Departments of Commerce, Homeland Security, and Transportation also play significant roles. Commercial space activities are not always in support of national security or military functions, so representation from a well-rounded set of agencies will be necessary regardless.
Concluding Thoughts and Questions
From my perspective, the benefits from a CI designation may not provide the support industry representatives are hoping for. In order to offer valuable intelligence and threat reporting, risk management approaches, and methods for vulnerability reduction, greater effort is needed to clarify the critical elements of an emerging space industry. An overly broad delegation for commercial space would actually diminish the quality of federal support, as generalized feedback is less useful. Industry representatives, including the National Space Council Users’ Advisory Group, Aerospace Information Sharing & Analysis Organization, and the Space ISAC should help identify critical systems and assets for federal consideration. Clearer guidance will help establish boundaries of congressional oversight, prioritized government programs, and the nature of public-private partnerships.
Let us know what you think! Should commercial space systems get a standalone CI sector? Are we trending towards an oversaturated CI environment?
For more on related topics see: