The IT security market is popping Champaign corks today in celebration of the tremendous valuation placed on Mandiant. According to the New York Times, FireEye has agreed to pay $1 Billion in cash, stock and options for the Alexandria, VA, based Mandiant.
This is a 10x revenue valuation based on 2012 numbers. But Mandiant is a services company, best known for its breach response consulting and cleanup services. Ten times trailing revenue is extremely high for a services company. HP paid $13.9 billion for EDS in 2007 when it had revenue of an estimated $21 Billion. That’s a 0.66 multiple of revenue.
Looking closer at the deal there are several factors to consider. First, Mandiant’s 2013 revenue is probably much higher than its 2012 revenue which was 76% higher than its 2011 revenue. This past February Mandiant orchestrated a brilliant branding coup by publicizing evidence they had of a Chinese cyber espionage campaign, the now famous APT1 report. Attacks on the Washington Post and New York Times, also attributed to Chinese hackers led to Mandiant being called in to clean up the mess this year. This momentum most likely allowed Mandiant to at least come close to matching 2012’s growth, so instead of the $100 million figure it is reasonable to assume 2013 revenue of $176 million.
FireEye is putting $106.5 million in cash into the deal.
Next we have to look at the value of the stock and options that the investors and owners of Mandiant are due. The investors and executive leadership of Mandiant are savvy enough to recognize that FireEye’s stock valuation is in rarefied strata. At today’s $6.78 Billion market cap FireEye is way over priced compared to its competition. Even the $5 Billion valuation when the deal was struck is reminiscent of bubblier times.
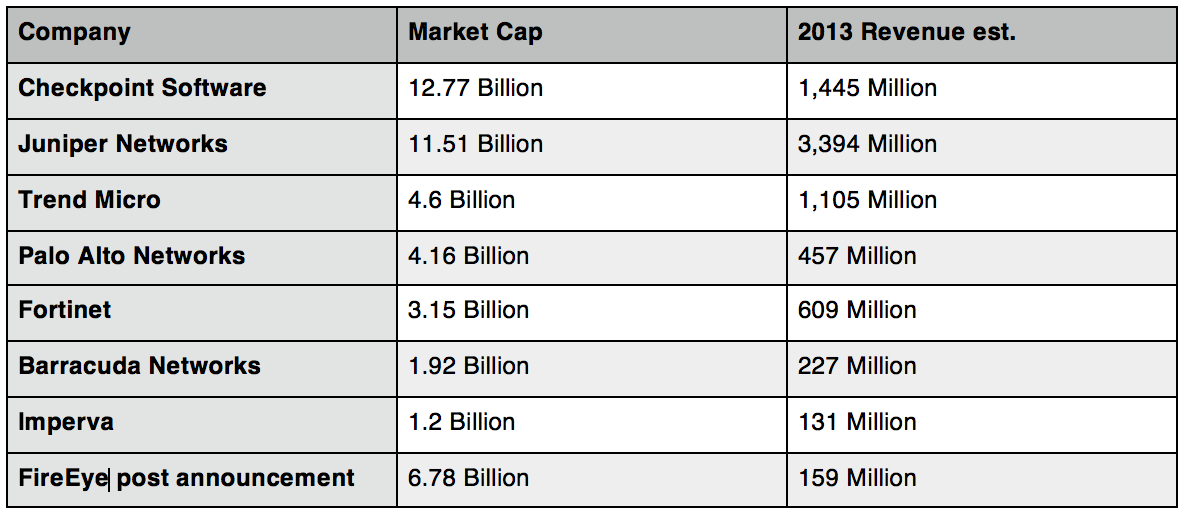
At $155 Million in projected 2013 revenue FireEye is just a little bigger than Imperva and smaller than Barracuda, another recently public security vendor. Yet Wall Street values FireEye more than Fortinet, Palo Alto Networks, or Trend Micro. Post deal announcement FireEye is valued at half of Check Point Software which has almost ten times the revenue.
FireEye’s strategy is clear. Use over-valued stock to acquire companies with revenue to feed Wall Street’s expectations of rapid growth. Organic growth for such a small company is going to be difficult, especially when its well entrenched competitors are introducing directly competing capabilities in their widely deployed platforms. Fortinet and Palo Alto have already introduced advanced malware defenses (virtualized sand boxes that “detonate” incoming executables to detect malware without signatures) within their firewall appliances. Trend Micro’s Deep Discovery is a stand alone advanced sand boxing environment that is instrumented to communicate malware discovery to the rest of the network.
Meanwhile Blue Coat has acquired Norman, arguably the most advanced sandboxing technology to incorporate into their security intelligence offerings.
So even if FireEye’s own product revenue flattens out, the rapid growth of services from Mandiant will allow them to continue demonstrating quarter over quarter growth.
Mandiant’s investors have gambled that their revenue and growth will prop up FireEye’s stock price, at least long enough for them to lock in their gains on stock and options.
But looking at FireEye in relation to the market it would be easy to assign a “true” value to it of something closer to Barracuda’s. That makes the $894 Million in stock and options realistically closer to $357 Million if the market ever catches up with reality.
Is this really a 10x valuation then? $463 Million in cash and stock for Mandiant at $176 million revenue is actually a 2.6 multiple.

