The Hudson Institute report on "Risking Apocalypse? Quantum Computers and the US Power Grid" highlights the significant threat posed by potential quantum computer attacks on the US power grid. It …
OODA CEO Matt Devost and OODA Network Members Review the OODA Almanac 2024 – Reorientation
Every year, we also use one of our monthly meetings for a discussion of the annual OODA Almanac with the OODA Network. This conversation took place at the February 2024 OODA Network Member Meeting – …
i-SOON Data Leak Is Interesting but Mostly Unsurprising
Recently, a major data leak was discovered on GitHub possibly exposing documents tied to the cyber spying activities of the Chinese company i-SOON. Although it is unclear if …
Continue Reading about i-SOON Data Leak Is Interesting but Mostly Unsurprising
Two Emergent and Sophisticated Approaches to LLM Implementation in Cybersecurity
Google Security Engineering and The Carnegie Mellon University Software Engineering Institute (in collaboration with OpenAI) have sorted through the hype - and done some serious thinking and formal …
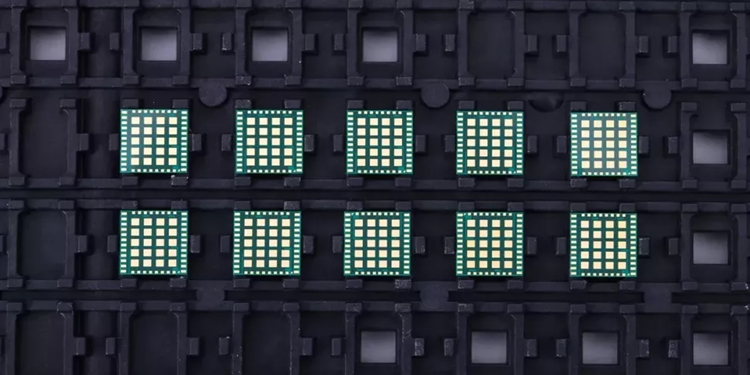
Two Chinese Supercomputers (with Mystery Hardware Components) Go Online
Conspicuous, controversial and notorious is the Chinese unwillingness to participate in global benchmarking list of the world's most powerful supercomputers. So, the "top 500" list goes out - with …
Continue Reading about Two Chinese Supercomputers (with Mystery Hardware Components) Go Online
Under Fire, CISA’s JCDC Continues Astride with 2024 Priorities
We have been very vocal boosters of CISA, the efforts of CISA leadership, and since its inception, the work of the Joint Cyber Defense Collaborative (JCDC). And we continue in our support of both …
Continue Reading about Under Fire, CISA’s JCDC Continues Astride with 2024 Priorities
The Future of the U.S. Defense Industrial Base: Challenges and Opportunities
The Congressional Research Service (CRS) is best in class research and analysis, judged against both public or private sector standards. In a recent report, the CRS broke down the vital questions …
Continue Reading about The Future of the U.S. Defense Industrial Base: Challenges and Opportunities
Are Global Stressors and Bank Failures Considered Strategically Net Positive by Some Market Players?
We take a look at the recently released Federal Reserve Board 2024 bank stress test scenarios, with an eye towards just how sensitive the stress tests are to disruptions and uncertainties created by …
Microsoft and OpenAI Issue a Stark Report and a $10M Bounty from the State Department
Competing cyber capabilities (on a spectrum from nation-state to non-state actors alike) and cyber-based conflict will continue to restructure, reformulate, and transform the very essence of what …
Global AI Developers Need to Set Some Standards – Now
Recently a collaboration between Microsoft and OpenAI found that nation state actors with ties to China, Iran, North Korea, and Russia have been engaged in leveraging artificial intelligence …
Continue Reading about Global AI Developers Need to Set Some Standards – Now