In late February, "the National Cyber Director (ONCD) released a report calling on the technical community to proactively reduce the attack surface in cyberspace. ONCD makes the case that technology …
The Drone Swarm Architecture Will Transform U.S. Warfighting Capacity
Lieutenant General (ret.) Clint Hinote, U.S. Air Force and Major General (ret.) Mick Ryan, Australian Army - Special Advisors to the Special Competitive Studies Project (SCSP) - have co-authored a …
Continue Reading about The Drone Swarm Architecture Will Transform U.S. Warfighting Capacity
Exponential Technology Stack Convergence: Generative AI-enabled Blockchain Networks
Throughout 2024, we expect disproportionate disruption when the exponential tech stack starts to converge. One of the most promising of these exponential technological intersections will be …
An End-to-End Neural Network is in Full Control of my Car: What does it mean for society?
Tesla just delivered a software update to my car that is so dramatically different that it is like having a new car. This post provides a bit more on why and extrapolates some lessons relevant to the …
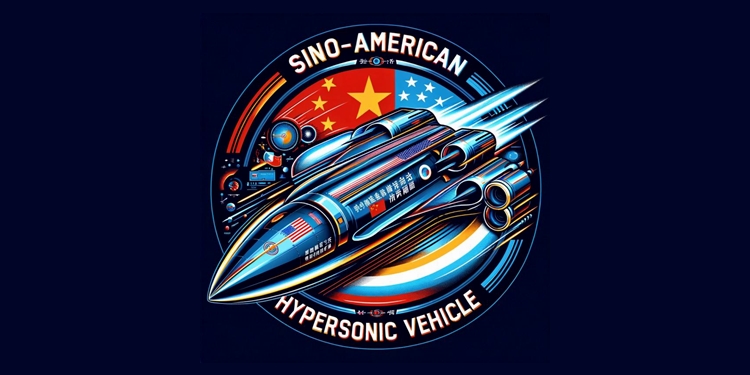
Hypersonic Vehicles are a Technological Tie that Binds U.S.-Sino Researchers
A report from the Frontier Assessments Unit is a deep dive into hypersonic vehicle research with a very specific framing: that of the collaborative efforts between U.S. universities and their …
Continue Reading about Hypersonic Vehicles are a Technological Tie that Binds U.S.-Sino Researchers
A Chip Alliance is Proposed by the U.S. as ASML Explores Foreign Expansion and New Market Rival Canon, Inc.
Europe's most valuable technology company, ASML Holdings, is responsible for the manufacturing of semiconductor machinery (the indispensable machines that make the chips). The chip-machinery maker has …
We Have a Privacy Executive Order! Time to See It in Action
In late February 2024, the Biden Administration issued its long-awaited Executive Order to protect the personal data of Americans from foreign threats by restricting access to Americans’ …
Continue Reading about We Have a Privacy Executive Order! Time to See It in Action
A ChatGPT Use Case for the Board of Directors: Corporate Disclosure and Policy Assessments
Researchers from the National Bureau of Economic Research (NBER) offer some foundational thinking on how ChatGPT can be applied to corporate disclosures and policies. According to the authors, this …
RAND Researchers Explore Scenarios for a U.S. Victory in a War with the PRC
Policy researchers from the Rand Corp. ponder the question: "How can the United States prevail in a limited war with the People's Republic of China (PRC) while avoiding catastrophic escalation?" Find …
Continue Reading about RAND Researchers Explore Scenarios for a U.S. Victory in a War with the PRC
An Overview of the NIST Cybersecurity Framework 2.0
The NIST Cybersecurity Framework (CSF) 2.0, an evolution of its predecessor, is a comprehensive guide designed to assist organizations across various sectors in managing and mitigating cybersecurity …
Continue Reading about An Overview of the NIST Cybersecurity Framework 2.0