The Olympic Games remain one of the most-watched events in the world, with billions tuning in across digital platforms and traditional broadcasting channels. Its high-profile nature makes it a target for malicious activity, but with the games’ increased digitization and with nation-state propaganda motives at play, cyberattacks are on the rise. As we approach the 2020 Tokyo Summer Games (24 July till 9 August 2020), it is essential to understand the risks and likely actors that will attempt to jeopardize the security and integrity of the upcoming Olympics.
This post begins with an overview of previous cyberattacks on the Olympic games and describe the actors that pose the greatest risk to cybersecurity. Next, it covers the cyber threat categories that should be prioritized by planning officials. Finally, it previews the types of future cyberattacks that are possible as officials continue to integrate technology into Olympic events.
History of Previous Olympic Cyberattacks
Since at least 2004, the International Olympic Committee, Olympic host nations, and commercial sponsors have experienced cyberattacks that target the games and its supporting digital infrastructure.
- 2004 Summer Olympics (Greece): In the run-up to the 2004 Summer Olympic Games, a team of skilled attackers were able to take advantage of a lawful intercept capability on Greece’s largest cellular service provider, Vodafone-Panafon. Later dubbed the “Athens affair,” attackers illegally wiretapped at least 100 high ranking officials, including Greece’s prime minister and his wife, his defense and foreign affairs ministers, top military and law enforcement officials, the Greek EU commissioner, U.S. diplomats, and journalists. A decade later, documents leaked by former NSA contractor Edward Snowden suggest that the U.S. was behind the attack.
- 2008 Summer Olympics (China): During the 2008 Olympics, China experienced approximately 12 million online alerts per day. Alarms were triggered on more than 12,000 devices across 70 venues in Beijing, however the security team was able to prioritize alerts to distinguish a bad configuration from attempts to hack the network.
- 2010 Winter Olympics (Canada): Malicious cyber activity was limited and the reported activities were categorized as low-risk, such as a spoofed copy of an official Vancouver Olympic website that distributed malware.
- 2012 Summer Olympics (England): The London Olympics witnessed 212 million malicious connection attempts and reported six major cyber incidents to the event leadership. Most of the significant incidents were DDoS attacks, like the 40-minute attack that tried and failed to take down power for the games’ opening ceremony.
- 2016 Summer Olympics (Brazil): Rio was a cybercrime hotspot during the 2016 Olympic Games. While attackers strayed from targeting Olympic infrastructure, criminals deployed malware to skim credit card information, demand ransom to unlock devices, and steal personal data from victims. Additionally, hactivist group Anonymous saw a resurgence in Brazil in the months leading up to Rio 2016. One month after the games, the World Anti-Doping Agency announced that a Russian government hacking group gained access to athletes’ medical data via spear-phishing. The group posted the personal information of hundreds of individuals in response to the recommendation that Russian athletes be banned because of doping.
- 2018 Winter Olympics (South Korea): The Olympic Games opening ceremony in PyeongChang was hit by a multifaceted cyberattack that led to disruptions to the Internet, broadcast systems, and the Olympics website. Many attendees were also unable to print tickets, leaving many of the seats empty during the most-followed event of the games. U.S. intelligence officials believe it was Russia who conducted the attack, while trying to make it look as if North Korea was behind the operation. The “false flag” is assumed to be continued retaliation for banning the Russian team from participating due to doping violations.
Threat Actors and Motivations
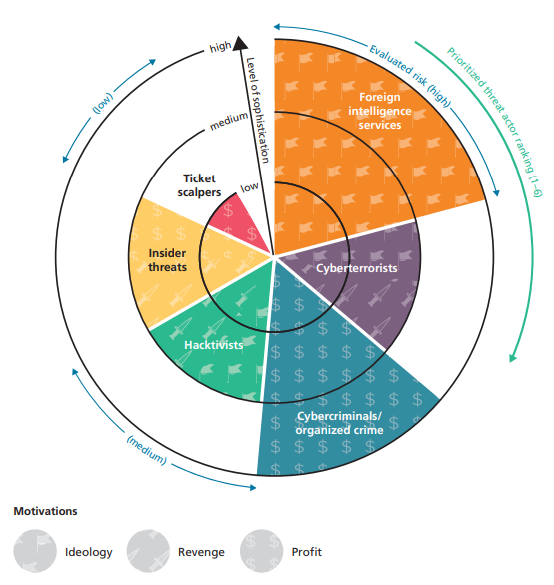
A recent RAND report characterizes 6 types of threat actors who pose the greatest risk to cyber infrastructure and networks for Tokyo 2020 planning officials. Their actions range in sophistication, risk level, and motivation as demonstrated by the figure below.
- Foreign Intelligence Services: These highly capable nation-state organizations have the resources to credibly threaten the cybersecurity goals of Tokyo 2020. They can intercept data, influence other threat actors to do the same, and hack into a host country’s networks.
- Cyberterrorists: Cyberterrorism has been defined by the Congressional Research Service as “the politically motivated use of computers as weapons or as targets, by sub-national groups or clandestine agents intent on violence, to influence an audience or cause a government to change its policies.” In the last decade, terrorist groups have been able to successfully use social media platforms to radicalize and recruit new members, direct attacks, and gather intelligence about potential targets.
- Cybercriminals and Organized Crime: Cybercriminals are typically in pursuit of financial or other material benefits. With the Olympics drawing in hundreds of thousands of international tourists, criminals will seek to take advantage of the influx. Furthermore, cybercriminals with links to North Korea have targeted Japan in the past and we can expect they will continue to do so.
- Hacktivists: These actors take part in hacking activities to demonstrate a political stance. During the 2016 Rio Olympics, Anonymous launched #OpOlympicHacking in protest. The operation targeted Brazilian government organizations, citing an increase in poverty and social inequities as preparations for the games continued. Multiple DDoS attempts were successful, although short lived.
- Insider Threats: Research suggests that insider threats are triggered by negative work-related experience to then use their knowledge or access to exploit internal networks. They are typically after revenge or profit, where even the disclosure of unclassified but sensitive information can have disastrous effects.
- Ticket Scalpers: Scalpers will use bots to automate the purchase and reselling of tickets at highly inflated rates. They have operated at previous Olympics, but their overall threat to the games’ cybersecurity is low compared to other actors.
High-Level Cyber Threats to Tokyo Olympics in 2020
Although Japan stated that they have made cybersecurity a top priority for their Olympic preparations, officials are still concerned the event has made Tokyo a target for hackers. The country has taken steps in the last few years to bolster its cyber defenses, to include introducing a new cybersecurity strategy and hacking its own citizens. However, will it be enough to prevent major cyber incidents during the 2020 Games? This will be an open question till the games begin.
An alert from Microsoft’s Threat Intelligence Center confirms that cyberattacks against the Tokyo Olympics have already begun. Russian government-sponsored hackers have targeted at least 16 national and international sporting and anti-doping organizations, successfully compromising a small subset of systems. The group responsible, also known as Fancy Bear, has previously targeted the same organizations in 2016 and 2018 to retaliate for allegations of cheating by Russian Olympic athletes. Ars Technica noted the actors used “spear-phishing, password spray, exploiting internet-connected devices and the use of both open-source and custom malware” to gain access, even “traveling to targets’ physical locations and hacking targets’ computer networks or hotel Wi-Fi connections.” Fancy Bear is believed to be a unit of Russia’s military intelligence agency, where previous cyberattacks consist of the hack against the Democratic National Convention during the 2016 U.S. Presidential election cycle and the costly NotPetya worm.
While Russian retaliation campaigns are likely to continue, we should still expect to see activity from a majority of the threat actors mentioned above. Planning officials should prioritize and prepare for the following high-level cybersecurity threats.
- Targeted attacks: These can be aimed at Olympic assets, individuals, or organizations for financial or political gain. They fall short of a desire to inflict physical harm on athletes or spectators, but rather wish to impose reputational or financial losses. Russia is a likely suspect to carry out additional cyberattacks, as demonstrated by the Olympic Destroyer malware used in 2018 to disrupt the opening ceremony in PyeongChang. Officials should also be on the lookout for DDoS attacks, as less sophisticated groups such as hacktivists can leverage them as well.
- Broad ransomware attacks: Ransomware attacks can be used to indiscriminately target a wide range of devices. Olympic information and communications technology infrastructure is at risk, where bad actors can choose to disturb competition events or steal information from participants, visitors, and point-of-sale systems. Criminals have been known to purchase cheap SSL certificates to “secure and encrypt data” using the https protocol (activating padlock at the beginning of the URL) to give the illusion that a website is legitimate. Alternatively, attackers may also create fraudulent sites to watch Olympic events and direct fans to unknowingly download malware.
- Disinformation/propaganda campaigns: Countries have long viewed the Olympics as a proxy for geopolitics. The Atlantic highlights the belief that authoritarian regimes love sporting events like the Olympics, as it operates as an important piece of propaganda for the home state to project power. “To be a true global power,” the article says, “you had to defeat your enemies in every arena.” Because reputational stakes are high, actors will take to social media in order to distribute misinformation or outright false statements to cause embarrassment for individuals, sponsors, or the host nation. These tactics could also result in more nefarious outcomes to cause panic or disrupt the Olympic Games themselves.
Final Thoughts
The past decade has witnessed increasingly sophisticated and brazen cyberattacks against Olympic infrastructure. A 2017 report by UC Berkeley’s Center for Long-Term Cybersecurity evaluated how the integration of technology into major sporting events, from digital display panels to artificial intelligence-based scoring software, increases the likelihood of cyberattacks. Though current attacks have focused on stadium IT systems and ticket sales, future attempts may diminish the integrity of the results or worse, enable terrorist attacks for worldwide broadcast. The report posits future headlines, like the ones below, where Olympic athletes’ accounts are hacked to retrieve personal data or terror groups attempt to compromise security systems to initiate a physical attack.
As the threat of cyberattacks continue to increase, Olympic host countries need to remain vigilant as a successful high-impact attack has yet to be realized. Security planners need to incorporate cybersecurity as a goal early on and integrate strong defensive strategies to hamper attacks before they are able to take place on the world stage.
What should be done about these threats? Here is our take:
- Your threat model should drive your actions. As the host country, Japan should take strategic action to enhance their infrastructure to make it harder for nations to attack and build in operational capabilities to detect and respond to attacks. Participating teams should have individual training on how to reduce risk of compromise. The Olympic Committee should lead in ensuring all game functions are resilient to attack, as well as the back office functions. Journalists should ensure they are following best practices in cyber defense, as should the spectators.
- Exercise your intentions. Your plan needs to be exercised in advance. This will help reduce chaos in crisis and identify gaps that need addressing before the Olympics start.
- Ensure your entire team has appropriate information. We are big believers in intelligence driven operations. Ensure everyone is informed of the situation and knows where to turn for more info. We want to be a part of that and encourage you to sign your entire team up for the OODA daily pulse, but you will need to consider your own tailored intelligence feeds to the key decision-makers in your organization.
For more defensive measures see: